Joeseph Redmon, who invented the YOLO Algorithm, quit his research over ethical concerns. These are some dark shadows this is throwing ahead.
Tag: computer
-
Apollo 11 Guidance Computer vs. USB-C
Apollo 11 Guidance Computer vs. USB-C: It could be that USB-C Cables nowadays have more compute capacity than Apollo 11 had on it’s way to the moon. Forrest Heller(?) made an effort to compare the technical specs and put them into perspective.
-
British Royal Mail issues computer games stamps
British Royal Mail issues computer games stamps writes BoingBoing:
BoingBoing.net 
Worms, Wipeout, Micromachines & Sensible Soccer The article features pictures of these stamps. Those who remember the times will find these adorable. The stamps are apparently available as first or second class stamps, at £1.60 or £1.55, and also in collectors sets.
Do I know enough people in the UK to send me postcards with stamps from:
- Elite(1984)
- Dizzy (1987)
- Populous (1989)
- Lemmings (1991)
- Micro Machines (1991)
- Sensible Soccer (1992)
- Wipeout (1995)
- Worms (1995)

Lemmings, Popoulus, Dizzy and Elite each? Germany, meanwhile, is still debating whether computer games are hazardous and the people involved in the scene should be observed.
-
The Mind at Work: Guido van Rossum on how Python makes thinking in code easier
Python, the programming language, gained lot’s of popularity only in the past decade. In particular for big data applications, machine learning and data science the language is almost without alternative. But also for tool development or web applications backends, Python has huge adoption. Reasons are it’s huge ecosystem and a friendly, constructive community. Despite it’s newer competitors it has been around for 30 years. One of the most appreciated benefits is the steep learning curve, that allows virtually everyone to understand Python code.
Dropbox has an interview with Guido van Rossum, who published the first version of the language in 1989. The conversation revolves around the purpose of code and how python helps improve cooperation and productivity.
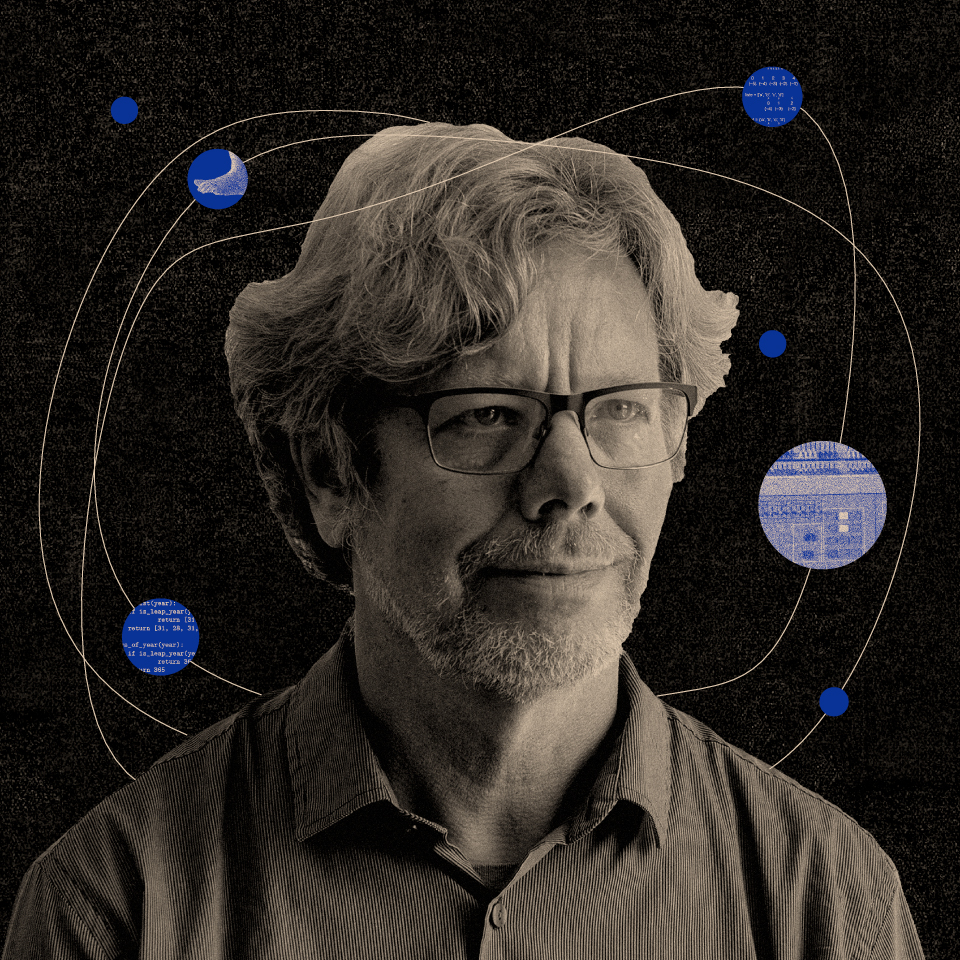
Guido van Rossum “You primarily write your code to communicate with other coders, and, to a lesser extent, to impose your will on the computer.”
Guido van RossumA conversation with the creator of the world’s most popular programming language on removing brain friction for better work. Source: The Mind at Work: Guido van Rossum on how Python makes thinking in code easier
-
Categories of Computer Crimes
Breach of data security: Information stored on network or computers is altered by attackers. Breach of operations security: Attackers take advantage of vulnerabilities within daily procedures to access or alter information through methods like password sniffing. Breach of personnel security: Sensitive company information is gained from an employee by attackers Breach of communication security: Information is being intercepted or altered on the way across a network. Breach of physical security: Attackers gain access to a building or to computer/networking hardware. Computer as an instrument. Attackers use computers to steal or commit fraud. Crimes associated with the prevalence of computers. Attackers illegally use or sell computer components, software and information. Computer as the target. Attackers disrupt or damage computers and networks, or steal data stored on computers. Computer as incidental to other crimes. Attackers may use computers to facilitate crime or to make crime difficult to detect. -
Securing Cyberspace in the 21st Century
Cybersecurity has emerged as an area of intense research activity that endeavors to protect cyberspace, enabling it to continue to function as required even when subjected to cyberattacks.
-
Computing Now: Toward a Science of Security – IEEECS
January Theme in Computing Now: Toward a Science of Security.
via Computing Now Archive | January 2013
-
Computer Society: Webinar
Computer Society bietet am Dienstag, 18. September 2012, ein Webinar über Security und Compliance in der Cloud an. Anmeldung: Maintaining Security & Compliance as IT Services Move to the Cloud.